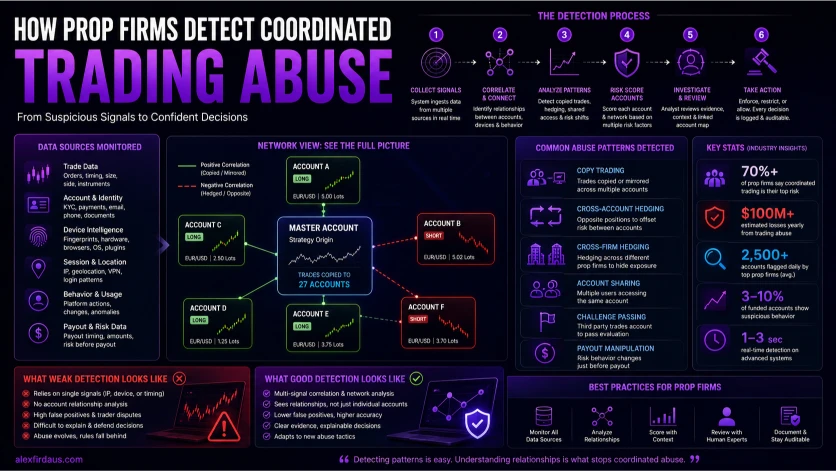
Prop firms detect coordinated trading abuse by comparing trade timing, account links, device signals, session history, exposure, payout behavior, and repeated relationships between accounts. Good detection looks for connected patterns, not one suspicious trade.
The simple question is: “Did this account break a rule?”
The better question is: “Does this account behave like part of a wider network?”
That difference matters.
Most coordinated abuse does not look extreme inside one account. A single account can look normal. The pattern becomes clearer only when the firm compares accounts, trades, devices, sessions, access history, exposure, and payout behavior together.
That is where many prop firms get it wrong.
They look for isolated triggers:
- Same IP address
- Similar trade timing
- Same device
- Opposite positions
- Unusual payout timing
- High trade similarity
Those signals matter, but none of them should become a verdict by itself.
A fair detection system asks a deeper question:
“Are these accounts controlled, influenced, or coordinated by the same person, group, software, or third-party service?”
That is the core of coordinated trading abuse detection.
Public rulebooks already show how broad the problem is. FTMO x OANDA’s forbidden trading practices prohibit simulated trades done alone or in concert with other people, including connected accounts, accounts held with different providers, and opposite positions used for manipulative purposes. The same rules also prohibit third-party access and third-party trading on behalf of another user.
That is the real line.
The problem is not that two traders had one similar idea.
The problem is coordinated control.
Tools like QuantSentry fit this conversation because the serious problem is no longer basic rule-breaking. It is connected-account behavior that firms need to detect, review, and explain.
What is coordinated trading abuse in prop trading?
Coordinated trading abuse happens when a person, group, service, or system uses multiple accounts to bypass rules, reduce real market risk, pass challenges, or multiply payouts without independent trading decisions.
This includes several patterns that often overlap:
- Copy trading networks
- Cross-account hedging
- Cross-firm hedging
- Challenge passing services
- Account sharing
- Multi-accounting
- Third-party account management
- Payout cycling
These are not always separate tactics.
A challenge passing service can use a trade copier. A copier network can involve account sharing. A multi-account group can use cross-account hedging. A trader can pass an evaluation with one person’s help, then trade the funded account differently after passing.
That is why a simple banned-practices page does not solve the problem.
The firm needs to know whether each account reflects independent trading behavior.
For example, one trader and another trader can both buy gold during a high-volume session. That does not prove abuse. Many traders watch the same instruments, sessions, news events, and price levels.
But if twenty accounts enter the same instruments in the same sequence, with similar lot ratios, similar exits, shared access signals, and payout requests around the same stage, the firm has a stronger reason to investigate.
The goal is not to punish similarity.
The goal is to identify coordination.
For background on how the broader prop model works, see my guide to prop firms 101.
QuantSentry
Seeing suspicious accounts? You need to see the network.
Purpose-built detection for prop firms. Linked accounts, copied trades, hedging patterns — one workflow.
No pitch deck. A direct look at your data.
How do prop firms detect copy trading?
Prop firms detect copy trading by comparing trade sequences across accounts, including entry time, exit time, symbol choice, direction, lot size ratios, stop-loss distance, take-profit distance, duration, and repeated similarity over time.
A single matching trade proves very little.
A repeated sequence proves more.
A trade copier usually leaves patterns because trades move from a lead account to follower accounts. TopstepX’s copy trading documentation describes a setup where a lead account controls follower accounts, and follower accounts cannot independently create, close, or adjust orders while copy trading is enabled.
That gives firms several things to compare:
- Did the same symbol appear across accounts?
- Did the orders appear in the same direction?
- Were entries close together?
- Were exits close together?
- Did lot sizes follow a stable ratio?
- Did stops and targets match?
- Did the same sequence repeat across days?
- Did the accounts share access, device, identity, or payout signals?
The most important word is “repeat.”
One copied-looking trade can happen by chance. A repeated pattern across many trades is harder to explain as coincidence.
A simple example:
- Account A buys EUR/USD
- Account B buys EUR/USD three seconds later
- Account C buys EUR/USD five seconds later
- All three exit within ten seconds of each other
- The same sequence repeats on gold, NASDAQ, and GBP/USD
- Lot sizes stay proportional across accounts
That looks less like three independent traders and more like one decision being distributed.
The firm still needs supporting evidence before enforcement. But the pattern deserves investigation.
Is trade copying always abuse?
Trade copying is not always abuse. Some firms allow it in specific account setups, but it becomes abusive when it hides third-party control, coordinates multiple traders, creates cross-account hedging, or multiplies payouts without independent decision-making.
This is where traders often get confused.
A tool can be allowed, but a use case can still be prohibited.
Topstep, for example, supports copy trading inside its own platform, but its hedging guidance still warns traders to avoid coordinating positions across accounts or using copy trading tools in ways that create opposite exposure.
That distinction matters.
Allowed use usually looks like this:
- A trader copies their own trades across permitted accounts
- The firm allows that setup
- The copied trades stay inside the permitted environment
- There is no cross-account hedging
- There is no hidden third-party control
Abusive use looks different:
- A group copies one signal across many accounts
- A passing service controls client accounts
- One account takes the long side while another takes the short side
- Accounts are split across different users or identities
- The copier multiplies payout opportunities from one strategy
The copier is not the whole issue.
The real issue is whether the accounts represent independent trading decisions.
How do prop firms detect cross-account hedging?
Prop firms detect cross-account hedging by looking for opposite positions across linked accounts. They compare timing, position size, instrument correlation, duration, account relationships, and whether one account absorbs loss while another moves toward payout.
Cross-account hedging is one of the clearest forms of coordinated trading abuse.
A trader or group opens a long position on one account and a short position on another. One account wins. One account loses. If the losing account stays within drawdown or gets sacrificed, the winning account can move toward payout.
That does not show independent trading skill.
It shifts risk across accounts.
I covered the trader-side concept in my article on prop firm hedging, but the operator-side problem is different. The firm has to decide whether opposite positions came from independent traders or from one coordinated setup.
The strongest detection signals include:
- Opposite positions on the same instrument
- Opposite positions on correlated instruments
- Similar entry timing
- Similar position size or exposure
- Similar exit timing
- Shared devices, IPs, payment details, or session patterns
- One account moving toward payout while another absorbs drawdown
- Repeated long-short pairing across accounts
The logic is not unique to prop firms. CME Group’s Rule 534 advisory explains how buy and sell orders across accounts with common beneficial ownership can become prohibited wash trades when the purpose is to avoid genuine market risk. Prop firm programs are not the same as regulated futures markets, but the risk-removal logic is similar.
If accounts are controlled together to remove real exposure, the result does not represent independent trading.
That is why cross-account hedging detection should focus on exposure, not only symbols.
A weak system asks:
“Did Account A buy EUR/USD while Account B sold EUR/USD?”
A stronger system asks:
“Did these accounts create offsetting exposure across the same or related instruments, at connected times, with evidence that the accounts are linked?”
That is a better question.
How does cross-firm hedging make detection harder?
Cross-firm hedging is harder to detect because the opposite positions sit with different prop firms. Each firm sees only one side of the risk, so detection needs shared intelligence, vendor networks, payout analysis, and account-relationship signals.
Inside one firm, cross-account hedging is easier to detect because the firm can compare both accounts directly.
Cross-firm hedging hides the other side.
Example:
- Account A at Firm 1 buys NASDAQ
- Account B at Firm 2 sells NASDAQ
- One account wins
- The other loses
- The trader or group keeps the payout from the winner
Firm 1 sees only the long trade. Firm 2 sees only the short trade. Neither firm sees the full structure unless it has access to shared risk intelligence or enough connected signals to spot the broader pattern.
That is why organized groups often prefer cross-firm hedging.
It separates the evidence.
Detection usually depends on:
- Abnormal pass rates
- Repeated high-risk payout behavior
- Shared device or session signals
- Similar evaluation timing
- Repeated strategy patterns across known clusters
- Vendor-side risk intelligence
- Shared infrastructure between firms
- Manual review after payout anomalies
This is also where network-based detection becomes more useful than normal rule matching.
A rule engine works inside one account.
A network engine looks for relationships.
Why do most prop firms get abuse detection wrong?
Most prop firms get abuse detection wrong because they treat coordinated abuse as a single-account rule breach. The real problem is relationship-based and spread across accounts, devices, sessions, trade behavior, exposure, and payout timing.
This creates two problems at the same time.
First, firms miss sophisticated abuse.
Basic copier abuse is easy to catch. Entries match. Exits match. Lot sizes match. The same order comments appear. The accounts move together.
Organized groups adapt.
They use delays. They vary lot sizes. They split accounts across firms. They change symbols. They rotate accounts. They use different VPS setups. They avoid perfect matching.
A static rule misses that.
Second, firms create false positives.
A shared IP does not prove abuse. Similar trades do not prove abuse. VPS use does not prove abuse. Trading the same instrument during the same session does not prove abuse. Two profitable traders can trade similar setups without being connected.
This is why single-signal enforcement is dangerous.
A signal should trigger review, not replace review.
Bad detection asks:
“Did two accounts do something similar?”
Good detection asks:
“Do multiple independent signals show these accounts are linked or coordinated?”
That is the difference between risk management and guesswork.
Need help reviewing suspicious account networks?
Prop firms dealing with copy trading, cross-account hedging, account sharing, challenge passing, or payout-stage abuse need more than another rule alert. They need an investigation layer that connects signals across accounts, trades, devices, sessions, and payouts.
QuantSentry is built for that use case. It helps risk teams review linked accounts, copied trades, hedging patterns, access signals, and evidence trails before making enforcement decisions.
What signals should prop firms compare before enforcement?
Prop firms should compare trade behavior, account relationships, device signals, session patterns, exposure, payout timing, and identity consistency before serious enforcement. One weak signal should start investigation, not end it.
Here is a simple way to think about signal strength:
| Signal | What it can show | Why it is not proof alone |
|---|---|---|
| Shared IP | Possible account cluster or shared access | Mobile networks, coworking spaces, households, and VPS setups can overlap |
| Similar trades | Possible copy trading or signal following | Traders can watch the same instrument, news event, or price level |
| Same device | Possible account sharing or passing service | Shared devices and technical tools can create messy data |
| Opposite positions | Possible cross-account hedging | The firm still needs account-link and timing evidence |
| Payout timing | Possible payout cycling or abuse pattern | High-performing traders also request payouts |
| Strategy change | Possible challenge passing or account handoff | Traders can change style after funding |
The strongest cases combine multiple signals.
For example, a shared IP is weak by itself.
A shared IP plus repeated copied trades, proportional lot sizes, matching exits, linked payout timing, and account-stage behavior changes is much stronger.
That is how firms reduce false positives while still catching real abuse.
What is the difference between rule-based detection and network-based detection?
Rule-based detection checks whether an account triggered a fixed condition. Network-based detection studies relationships between accounts, trades, sessions, devices, exposure, and payouts. Rule-based controls catch obvious abuse, but network detection catches coordination better.
Rule-based detection is useful.
It can catch simple cases like:
- Same device used by many accounts
- Same trade copied across accounts
- Same IP shared across suspicious accounts
- Opposite positions on the same instrument
- Excessive server requests
- Known prohibited trading behavior
The problem is that rule-based systems are easy to over-trust.
A rule says, “Flag this.”
It does not always say, “This is abuse.”
Network-based detection is different. It builds a relationship map.
It checks:
- Which accounts behave together
- Which accounts share technical signals
- Which accounts trade the same sequence
- Which accounts take opposite exposure
- Which accounts change behavior after passing
- Which accounts request payouts after similar risk patterns
- Which accounts connect through devices, sessions, payments, or timing
That is closer to how mature surveillance works.
The CFTC’s market surveillance program is focused on protecting markets from fraud, manipulation, and abusive practices while preserving market integrity. Prop firms are not exchanges, but the mindset is useful.
The issue is not always market manipulation.
The issue is program manipulation.
QuantSentry
Rules flag accounts. Networks reveal abuse.
QuantSentry sits between alert and enforcement — connecting signals into cases your risk team can actually act on.
Free. No commitment.
Where does QuantSentry fit into coordinated abuse detection?
QuantSentry fits into coordinated abuse detection because the hardest cases are account-network cases, not single-account violations. It helps firms connect copied trades, hedging links, access signals, payout behavior, and evidence trails.
Most prop firms already have rules.
That is not the gap.
The gap is seeing how accounts relate to each other.
A rule-based system can flag a same-IP login, a similar trade, or an opposite position. That helps, but it still leaves the risk team with a harder question: are these isolated signals, or are they part of a coordinated abuse pattern?
That is where QuantSentry fits.
It sits in the investigation layer between alert and enforcement. Its value is not only finding suspicious activity. Its value is helping a firm understand why the activity looks suspicious, which accounts are involved, and how the evidence connects.
For coordinated trading abuse, a purpose-built tool should help operators see:
- Which accounts are linked
- Which trades were copied or mirrored
- Which accounts created opposite exposure
- Whether the same pattern repeated
- Whether device, session, or identity signals support the link
- Whether suspicious behavior appeared near payout
- Whether the case is strong enough for review or enforcement
That is the right role for QuantSentry in this article.
Not “QuantSentry catches all cheaters.”
Not “QuantSentry solves fraud.”
The stronger angle is this:
This is why QuantSentry is relevant. It treats abuse as a network problem, not a single-account rule problem.
That distinction is important. A tool that only flags accounts can create more noise. A tool that explains relationships helps firms make better decisions, reduce false positives, and build stronger evidence before acting. QuantSentry does not remove the need for human judgment. It gives risk teams a clearer view of the account network so they can decide whether the pattern is coincidence, poor rule design, or coordinated abuse.
What signals should prop firms review before denying a payout?
A prop firm should review multiple independent signals before denying a payout. Trade similarity, device data, login behavior, account relationships, exposure patterns, and payout timing should support the same conclusion before enforcement happens.
Payout review is where trust breaks.
Traders hate vague payout denials. Firms hate paying coordinated abusers. Both sides have a point.
The fix is not weaker enforcement.
The fix is stronger evidence.
A weak payout denial sounds like this:
- “Suspicious activity detected”
- “Your trading resembles another account”
- “You violated our risk policy”
- “The decision is final”
That creates anger because it explains nothing.
A stronger investigation shows the category and evidence:
- Copy trading pattern
- Cross-account hedging pattern
- Account sharing evidence
- Third-party account management indicators
- Multi-account relationship
- Payout-stage risk displacement
A good payout review should ask:
- Which accounts are linked?
- Which trades created the suspicion?
- Did the same pattern repeat?
- Do device or session signals support the link?
- Was real risk reduced or shifted?
- Did the pattern appear near payout?
- Does the evidence support enforcement?
The key is independence.
If the only signal is a shared IP, the case is weak.
If the shared IP appears with repeated copied trades, proportional sizing, matching exits, and linked payout behavior, the case becomes stronger.
This is also part of the wider prop firm operating model. Firms are not only filtering traders. They are filtering behavior, incentives, and risk patterns. I covered that broader idea in The Pipeline Strategy.
How should prop firms handle device fingerprinting without false positives?
Device fingerprinting should support an investigation, not decide it alone. It becomes useful when paired with trade correlation, login history, behavior changes, payout timing, and account relationships across a longer pattern.
Device signals are powerful.
They can show when multiple accounts appear to come from the same machine, browser, VPS environment, or technical setup. They also help detect account sharing, passing services, multi-accounting, and device farms.
But device data can be messy.
A trader can use a third-party tool. A browser can create shared identifiers. A VPS setup can make accounts look connected. Multiple users can trade from the same location. Technical integrations can create unexpected overlap.
That is why device signals need context.
A device match should trigger questions:
- Did the accounts trade similar strategies?
- Did they enter or exit around the same time?
- Did they share payment or KYC signals?
- Did behavior change after evaluation?
- Did they request payouts in similar windows?
- Did one account offset risk from another?
If the answer is no, the firm should be careful.
This point matters because false positives damage trust.
A firm can be right about the risk category but wrong about the trader. That is why every serious detection program needs human review and an audit trail.
How do challenge passing services create detection signals?
Challenge passing services create detection signals because the account often changes behavior between registration, evaluation, funding, and payout. Firms can detect this through device changes, IP shifts, session timing, strategy drift, and trade behavior changes.
Challenge passing is simple in concept.
A trader buys a challenge. A third party logs in. The third party trades the account through the evaluation. The account is handed back after passing or after funding.
This is usually covered under account management rules.
The firm’s issue is not only that someone helped. The issue is that the evaluation no longer measures the registered trader.
Common signals include:
- New device after purchase
- New device after passing
- New IP region during evaluation
- Different trading hours after funding
- Different symbols after funding
- Different position sizing after funding
- Different trade duration after funding
- Sudden behavior change near payout
FTMO x OANDA says users must not allow third parties to access or use their accounts, and must not cooperate with third parties to perform simulated trades for them. That rule matters because challenge passing depends on exactly that kind of third-party control.
But again, detection needs layers.
A trader traveling after passing does not prove challenge passing. A different device does not prove challenge passing. A new strategy after funding does not prove challenge passing.
The case becomes stronger when several changes happen together.
What role does platform security play in prop firm abuse detection?
Platform security matters because weak authentication, authorization, session handling, and server-side validation make abuse easier. But most coordinated abuse still happens through valid logins and valid trades, so behavioral detection is still needed.
This is where some articles get the framing wrong.
Prop firm fraud is not only a web security problem.
It is a behavior problem, identity problem, account graph problem, and trade surveillance problem. Platform security is one part of the stack.
Strong platform security should include:
- Proper authentication
- Strong authorization on account-level actions
- Secure sessions
- Server-side trade validation
- Audit logging
- Rate limiting on sensitive actions
- Protection against replay or tampered requests
- Monitoring for suspicious API behavior
OWASP’s 2023 API Security Top 10 ranks Broken Object Level Authorization as the top API security risk. That matters for prop trading platforms because endpoints handling account IDs, trade records, payout records, or user permissions need strict object-level authorization.
Still, most abuse does not require hacking anything.
A challenge passer can use a valid login.
A copier group can place valid trades.
A hedging ring can use normal order placement.
That is why platform security and behavior detection need to work together.
What should a proper prop firm abuse-detection stack include?
A proper abuse-detection stack should include identity checks, device intelligence, session monitoring, trade correlation, exposure analysis, cross-firm risk signals, payout review, analyst workflows, and audit trails.
Here is the cleanest structure.
Identity and account integrity
This layer checks whether the account is likely controlled by the registered trader.
It includes:
- KYC consistency
- Payment method consistency
- Profile changes
- Account ownership signals
- Suspicious account clusters
- Account management indicators
Device and session intelligence
This layer checks how the account is accessed.
It includes:
- Device fingerprinting
- Browser fingerprinting
- VPS and proxy indicators
- Login geography
- Session timing
- Device changes after passing
- Multiple accounts from similar environments
Trade correlation
This layer checks whether accounts trade alike.
It includes:
- Entry timing
- Exit timing
- Symbol sequence
- Trade direction
- Lot ratios
- Stop-loss distance
- Take-profit distance
- Trade duration
Exposure and hedging analysis
This layer checks whether accounts reduce or shift market risk together.
It includes:
- Opposite positions
- Correlated instrument exposure
- Paired account risk
- Drawdown sacrifice patterns
- Payout-side concentration
- Repeated long-short structures
Payout-stage investigation
This layer checks whether suspicious behavior appears around rewards.
It includes:
- Payout request timing
- Sudden risk changes
- Account behavior after passing
- Consistency with evaluation behavior
- Linked account payout patterns
- Manual review of large or unusual payouts
Evidence and enforcement
This layer turns detection into a defensible decision.
It includes:
- Analyst notes
- Evidence snapshots
- Account relationship maps
- Trade logs
- Decision history
- Appeal support
- Exportable reports
This final layer is where many firms fail.
They detect something suspicious, but they cannot explain it clearly.
That is not good enough.
How can prop firms reduce false positives while still catching abuse?
Prop firms reduce false positives by using layered signals, longer behavior windows, explainable evidence, and human review before serious enforcement. Similar trades or shared technical data should start investigations, not automatically end them.
False positives are expensive.
They create support load, public complaints, review-site damage, social media disputes, and lower trust from legitimate traders.
False negatives are expensive too.
They let coordinated groups extract payouts from a system they are not genuinely passing.
The answer is not soft enforcement.
The answer is better evidence.
A good workflow looks like this:
Step 1: Trigger the alert
The system detects unusual similarity, opposite exposure, device overlap, or payout-stage behavior.
Step 2: Expand the context
The system checks related accounts, sessions, devices, trades, payments, behavior changes, and payout timing.
Step 3: Classify the pattern
The risk team decides whether the case looks like copy trading, hedging, account sharing, challenge passing, multi-accounting, or platform abuse.
Step 4: Review the evidence
An analyst checks whether the signals are independent and strong enough.
Step 5: Decide action
The firm takes no action, requests clarification, monitors the account, restricts the account, removes trades, denies payout, or terminates the account.
Step 6: Keep an audit trail
The firm records what was detected, why it mattered, and who approved the decision.
That structure protects the firm and the trader.
It also improves consistency across enforcement decisions.
What should traders understand about copy trading, hedging, and account sharing?
Traders should understand that prop firms usually care less about one isolated action and more about coordinated control. If accounts share decisions, access, exposure, or payout behavior, firms can treat the activity as abuse.
The safest rule is simple.
Trade your own account.
Do not let someone else pass your challenge. Do not share account access. Do not copy group signals into a funded account if the firm prohibits coordinated trading. Do not hedge risk across accounts. Do not assume that a trade is allowed just because the platform accepted the order.
Execution approval is not policy approval.
Many firms review behavior after the fact, especially near payout. That frustrates traders, but it also makes sense. A single trade rarely proves much. A pattern across time does.
Before using a copier, trader group, account manager, EA, or funded account service, traders should check:
- Does the firm allow it?
- Does the setup involve another person controlling the account?
- Does it copy trades from a master account?
- Does it create opposite exposure across accounts?
- Does it make the account look independent when it is not?
- Would the trader be comfortable explaining it during payout review?
If the answer is no, the risk is obvious.
What is the best way for prop firms to detect abuse without losing trader trust?
The best way is to combine network detection, clear rule categories, explainable evidence, and human review. Firms should detect abuse aggressively, but serious enforcement should require more than one weak signal.
Prop firms need clearer categories.
Not every suspicious case should be called “fraud.” That word is too broad and often too inflammatory.
Better categories include:
- Copy trading abuse
- Cross-account hedging
- Cross-firm hedging
- Third-party account access
- Challenge passing
- Account sharing
- Multi-accounting
- Payout manipulation
- Platform exploitation
These categories help traders understand the rule. They also help support teams explain decisions.
A good enforcement decision should answer five questions:
- What behavior was detected?
- Which accounts were involved?
- Which signals support the relationship?
- Did the behavior reduce or shift market risk?
- Is the evidence strong enough to defend the decision?
If the firm cannot answer those questions, it needs more review.
This is also why tools like QuantSentry are relevant. The goal is not to automate accusations. The goal is to give operators a better view of connected behavior.
Better evidence creates better enforcement.
Better enforcement creates more trust.
Why does network-based detection matter for the future of prop trading?
Network-based detection matters because coordinated abuse is a relationship problem. Copy trading, cross-account hedging, cross-firm hedging, account sharing, and challenge passing all become clearer when accounts are analyzed as connected patterns.
The prop industry is not dealing with one type of abuse.
It is dealing with a system of behaviors that often reinforce each other.
A trader can use a challenge passing service. That service can use a copier. The copier can distribute trades across many accounts. Some accounts can hedge others. The winning accounts can request payout. The losing accounts can be discarded.
A single-account review will miss too much.
A static rule will miss too much.
A vague payout review will anger too many legitimate traders.
The firms that improve will build detection around relationships.
They will combine:
- Trade correlation
- Cross-account exposure analysis
- Cross-firm risk signals
- Device intelligence
- Session monitoring
- Behavioral consistency checks
- Payout-stage review
- Explainable evidence
- Human review
That is the new standard.
The question is no longer whether prop firms can detect obvious copy trading.
The question is whether they can separate real coordination from normal trader overlap.
That is where most firms still struggle.
And that is why a purpose-built network-detection approach deserves serious attention.
The next step is looking at how this works in practice. That is where the QuantSentry review comes in, because the real question is not whether prop firms need better detection. They do. The real question is whether QuantSentry gives operators enough evidence to make fair, defensible decisions.
Need better evidence before payout decisions?
QuantSentry helps prop firms review linked accounts, copied trades, cross-hedging patterns, access signals, and payout-stage risk in one investigation workflow.
Book a Free QuantSentry Demo →FAQs
How do prop firms detect copy trading?
Prop firms detect copy trading by comparing trade timing, symbol choice, direction, lot size ratios, stop-loss placement, take-profit placement, trade duration, and repeated trade sequences across accounts. Strong systems also compare devices, sessions, and account relationships.
Can prop firms detect copy trading across different firms?
A single prop firm usually cannot see another firm’s full account data. Cross-firm detection depends on shared risk intelligence, vendor-side networks, shared infrastructure, anonymized signals, or repeated account behavior that appears across known clusters.
What is cross-account hedging in prop trading?
Cross-account hedging happens when linked accounts take opposite positions to reduce real market risk. One account can win while another loses, which lets the trader or group shift risk instead of trading independently.
What is cross-firm hedging?
Cross-firm hedging happens when opposite positions are placed at different prop firms. It is harder to detect because each firm sees only one side of the trade unless it has shared intelligence or network-level risk signals.
Is using a trade copier banned by prop firms?
Not always. Some firms allow trade copiers in specific setups. It becomes risky when the copier supports third-party control, coordinated group trading, cross-account hedging, or copied decision-making that violates the firm’s rules.
Is the same IP enough for a prop firm to ban a trader?
No. The same IP is a signal, not proof. A fair review should combine IP data with trade patterns, device signals, account relationships, session history, and payout behavior before serious enforcement.
Why do prop firms review accounts at payout?
Prop firms review accounts at payout because coordinated abuse often becomes clearer after multiple trades, account stages, and behavior changes. One trade rarely proves coordination, but repeated patterns across time can support a stronger case.
What is funded account abuse detection?
Funded account abuse detection is the process of reviewing suspicious behavior after a trader passes an evaluation. It includes detecting account handoffs, challenge passing, copy trading, cross-account hedging, and abnormal payout-stage risk behavior.
What is network-based abuse detection?
Network-based abuse detection analyzes relationships between accounts. It looks at trade similarity, opposite exposure, shared devices, session patterns, account history, payout timing, and behavioral clusters instead of reviewing each account alone.
Where does QuantSentry fit into prop firm abuse detection?
QuantSentry fits as an investigation layer for network-based abuse detection. It is most relevant when a firm needs to connect accounts, copied trades, hedging patterns, access signals, payout behavior, and evidence trails before making an enforcement decision.
Why do prop firms create false positives?
Prop firms create false positives when they treat one signal as proof. Similar trades, shared IPs, VPS use, or device overlap can have legitimate explanations. Strong enforcement needs several independent signals and human review.
What should a good prop firm detection system include?
A good system should include identity checks, device intelligence, session monitoring, trade correlation, exposure analysis, cross-firm risk signals, payout-stage review, evidence trails, explainable scoring, and human review.
Author
-
Alex started his career creating travel content for Jalan2.com, an Indonesian tourism forum. He later worked as a web search evaluator for Microsoft Bing and Google, where he spent over a decade analyzing search relevance and understanding how algorithms interpret content. After the pandemic disrupted online evaluation work in 2020, he shifted to freelance copywriting and gradually moved into SEO. He currently focuses on content strategy and SEO for finance and trading-related websites.
Recent Posts






